Android 12 引入了对单一注册模型的支持,以提供 MMTEL 和 RCS 功能。此模型允许设备通过设备的 ImsService 提供的单个 IMS 注册来管理所有 IMS 功能,并符合某些电信运营商引入的要求。与双注册模式在一台设备上管理多个IMS注册相比,单注册减少了运营商网络的流量并提高了可靠性。
Android 12 通过具有一组 API 的架构支持这种单一注册模型,这些 API 允许 AOSP 电话堆栈管理 ImsService 提供的ImsService功能和用户选择的 RCS 消息传递应用程序提供的 RCS 功能。为了支持 IMS 单一注册,设备制造商和 SoC 供应商必须实施这些 API 以在用户选择的 RCS 消息传递应用程序中启用 RCS 功能。
图 1 说明了使用 IMS 单一注册模型时设备的 IMS 堆栈。所有 IMS 应用程序通过单个 IMS 注册使用设备的默认 ImsService 来实现 MMTEL 和 RCS 功能。这包括供应、SIP 消息转发和 RCS 用户能力交换。
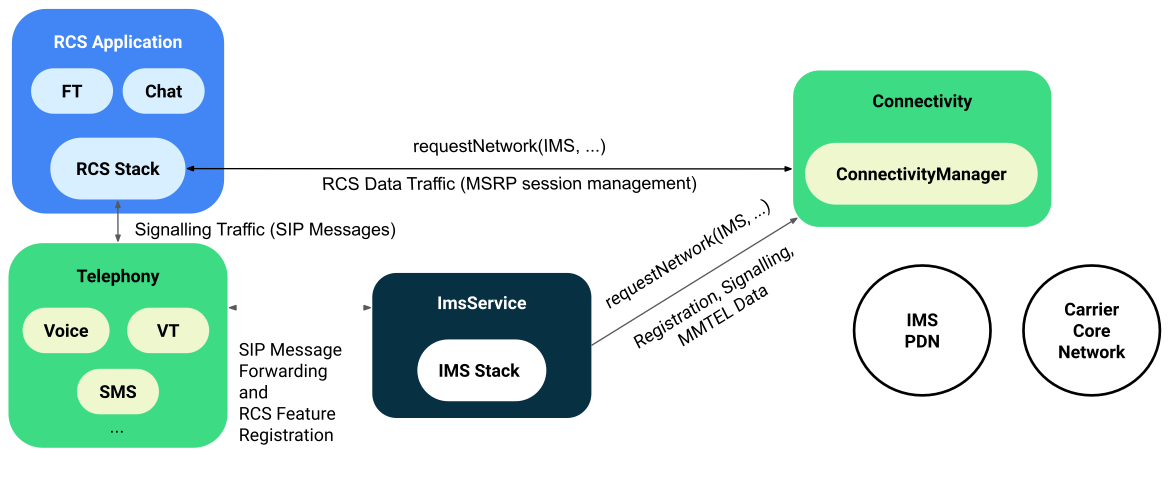
图 1.单一注册模型架构
Android 11 及更低版本仅支持提供 MMTEL 和 RCS 功能的双重注册模型,其中 MMTEL 由设备的 ImsService 提供,RCS 功能在顶部实现,并独立管理自己的 IMS 堆栈和与运营商网络的连接。
图 2 说明了双重注册模型的架构。在此模型中,每个应用程序负责连接到运营商的网络并为 MMTEL 和 RCS 功能建立 IMS 注册。设备的 ImsService 实现 MMTEL,使用设备的 IMS 数据连接到运营商网络,独立于其他 RCS 应用运行。
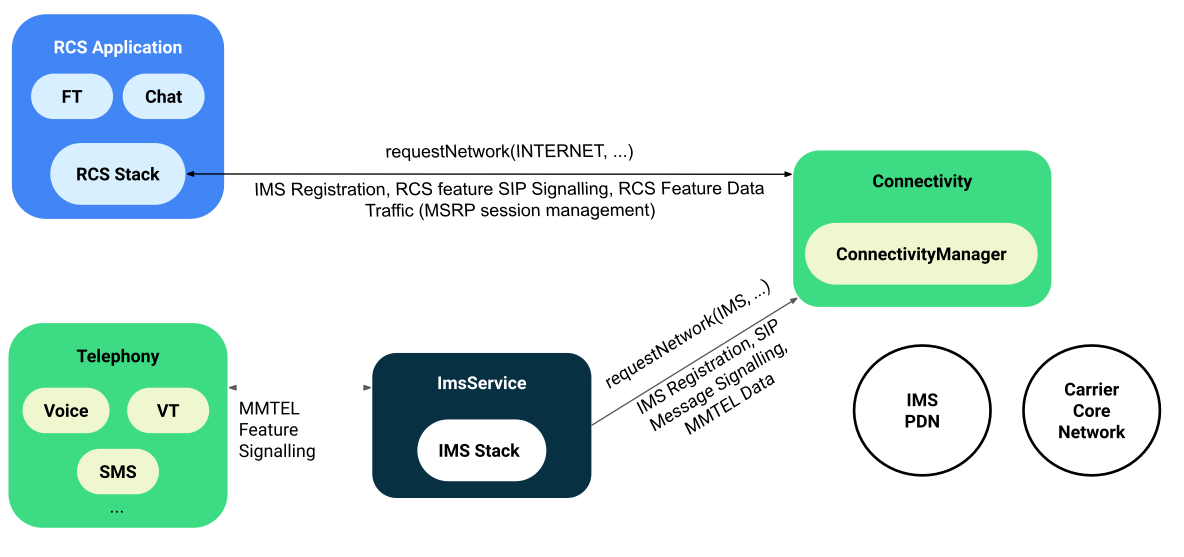
图 2.双注册模型架构
IMS 单一注册 API
需要 IMS 单一注册的运营商范围内的设备必须支持 IMS 单一注册 API 并定义 Android 功能PackageManager#FEATURE_TELEPHONY_IMS_SINGLE_REGISTRATION 。图 3 显示了支持 IMS 单一注册的 API。
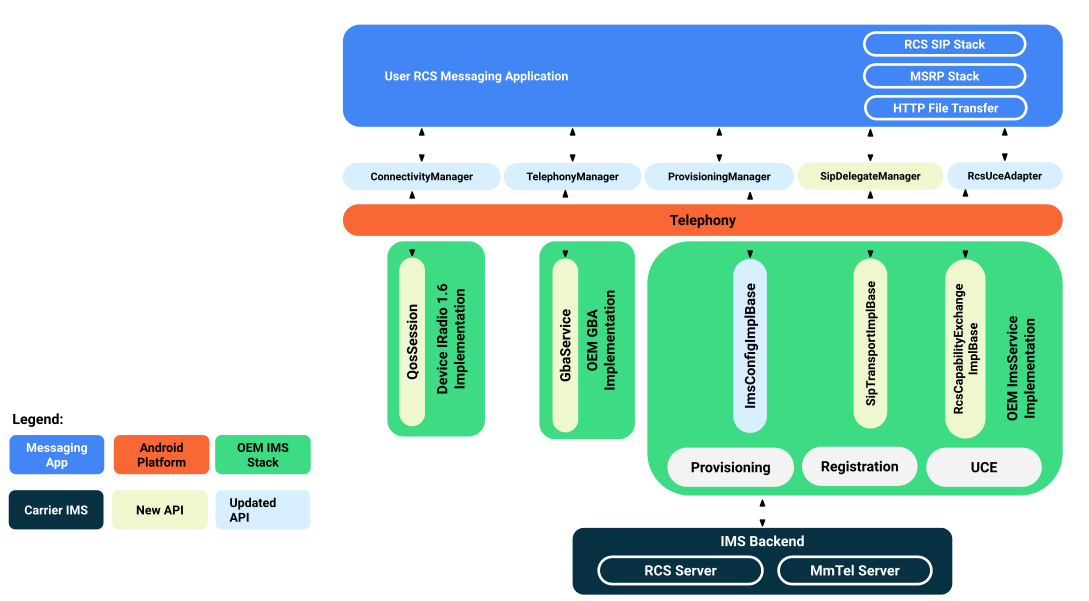
图 3.支持 IMS 单一注册的高级 API 表面
支持 IMS 单一注册作为 AOSP 电话堆栈的一部分的 Android 设备需要支持下表中描述的所有 AOSP API。
| API表面积 | RCS 应用程序 API | 供应商 IMS API | 描述 |
|---|---|---|---|
| RCS 配置 | 供应管理器 | ImsConfigImplBase | 如果运营商使用专有运营商授权机制,则允许 OEM 或运营商提供应用程序来更新 RCS 配置状态。 ImsService 还必须支持标准 AutoConfigurationServer (ACS),以便为不使用专有机制的运营商进行配置。 |
| SIP消息转发 | SIPDelegateManager | SipTransportImplBase | 允许 RCS 应用程序首先将特定的 RCS 功能标签与设备ImsService ,然后发送和接收与这些 RCS 功能标签关联的 SIP 消息和 IMS 注册更新。 |
| 专用承载通知 | 连接管理器 | 数据呼叫响应 | 允许应用在与特定本地端口关联的套接字上侦听 QoS 通知。 |
| GBA认证 | 引导认证请求 | Gb服务 | 允许 RCS 应用通过网络进行身份验证并访问用于 RCS 功能(如文件传输)的密钥。 |
| RCS用户能力交换 | ImsRcsManager | RcsCapabilityExchangeImplBase | 使 AOSP 能够将其 MMTEL 和 RCS 功能发送到供应商 ImsService,以便它们可以在一个实体下发布到网络以进行 RCS 用户能力交换。还允许对一个或多个联系人的 RCS 功能感兴趣的其他应用程序向网络查询联系人 RCS 功能。 |
安全和权限
Android 12 引入了以下权限,以确保对运营商网络和用户数据的安全访问:
-
android.permission.PERFORM_IMS_SINGLE_REGISTRATION -
android.permission.ACCESS_RCS_USER_CAPABILITY_EXCHANGE
android.permission.PERFORM_IMS_SINGLE_REGISTRATION权限必须由具有 RCS 功能的消息传递应用程序定义。要授予此权限,必须满足以下条件:
- 该应用程序必须作为特权应用程序安装,这意味着它已预安装在设备上并被允许访问特权权限
- 必须使用
RoleManager将应用设置为用户的默认 SMS 角色
如果不满足这两个条件,应用程序将被拒绝访问android.permission.PERFORM_IMS_SINGLE_REGISTRATION权限。这意味着第三方应用程序不允许访问 RCS 单一注册 API,因为它们需要设备上的运营商认证。
将android.permission.ACCESS_RCS_USER_CAPABILITY_EXCHANGE权限授予同样具有 READ_CONTACTS 权限的应用时,该权限允许应用使用RcsUceAdapter请求电话号码的 RCS 功能。要授予此权限,必须满足以下条件:
- 该应用程序必须作为特权应用程序安装,这意味着它已预安装在设备上并允许访问特权权限。
应用程序必须定义为以下
RoleManager角色之一:- 默认消息应用程序:由用户设置。
- 默认拨号器应用程序:由用户设置。
- 默认联系人应用:Android 12 中引入的角色,允许 OEM 通过设备覆盖值
config_systemContacts定义包名称,该名称必须与设备的联系人应用相对应。然后该应用程序被赋予联系人角色。
要使用ConnectivityManager访问 IMS APN 以设置和管理数据流量,应用程序还必须请求android.permission.CONNECTIVITY_USE_RESTRICTED_NETWORKS权限。
示例和来源
Android 在 AOSP 中提供了一个应用程序,它实现了一个测试消息应用程序,具有用于测试和开发目的的基本 RCS 消息传递支持。您可以在testapps/TestRcsApp找到该应用程序。当应用程序安装在设备上时,可以将其设置为用户的默认消息应用程序,并具有访问 IMS 单一注册 API 所需的权限。
Android 还为 RCS 提供了 ImsService 的示例实现。源代码位于/testapps/ImsTestService 。
执行
有关更多实施细节,请下载Android 中的 IMS Single Registration 。
验证
要验证 IMS 单一注册的实施,请执行以下操作:
- 确保CtsTelephonyTestCases CTS 测试套件通过。
- 安装并运行TestRcsApp以在集成期间运行基本的单一注册测试用例。
- IMS单一注册测试用例通过运营商认证。

